Organizations are embracing multiple public cloud platforms, resulting in increased complexity of management which impacts security and risk. Additionally, the built-in security tools that come with various cloud platforms are unique to each, compounding the challenge of consistently managing risk across all clouds in a multi-cloud world. This challenge renders security operations time consuming and ineffective. As the attack surface expands, organizations need to protect from not only from risks of configuration and management of the application elements themselves, but also from risks originating via cloud application programming interfaces (APIs) and UIs.
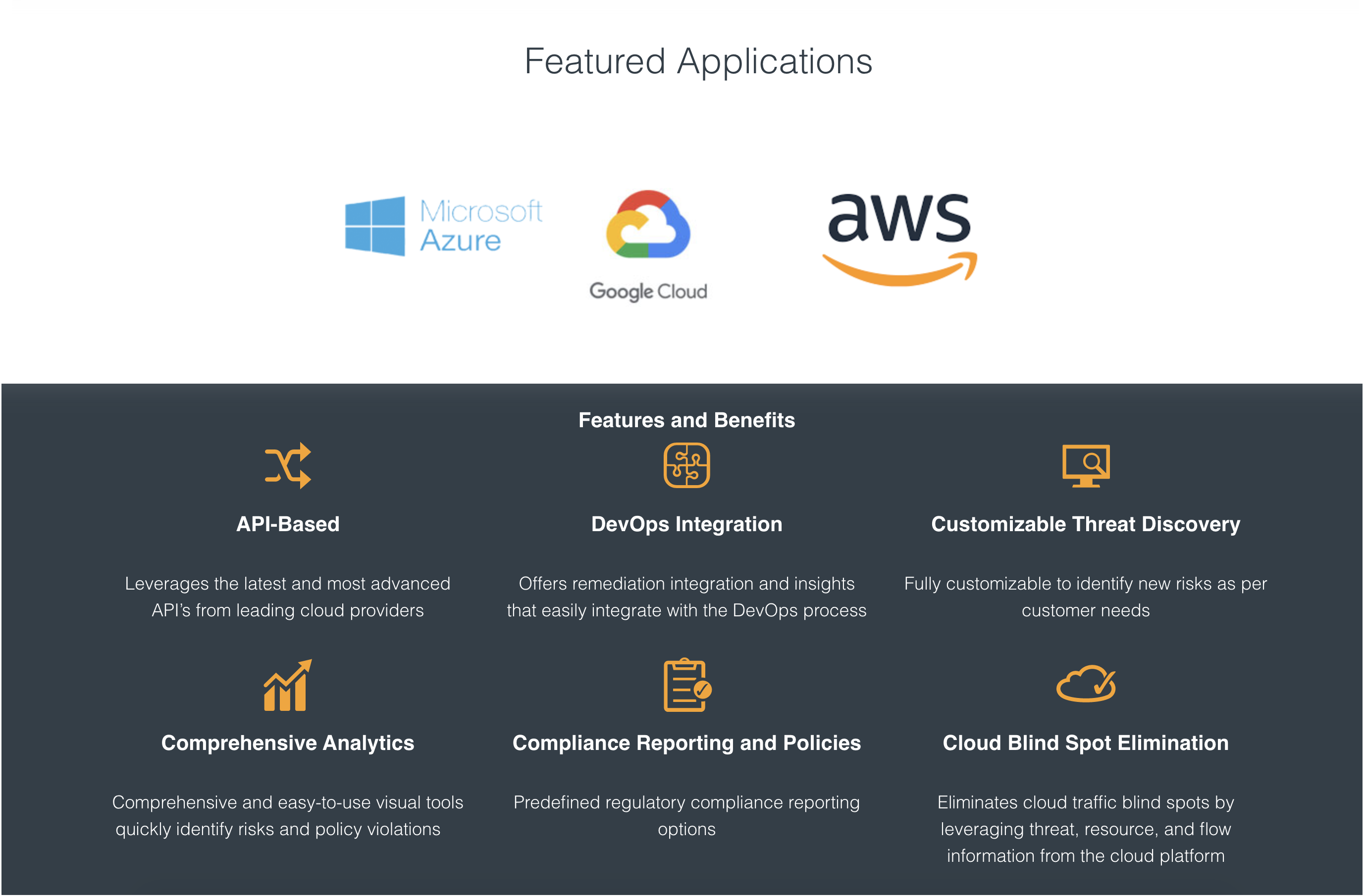
FortiCWP offers security administrators and DevOps teams the ability to evaluate their cloud configuration security posture, detect potential threats originating from misconfiguration of cloud resources, analyze traffic across cloud resources (in and out of the cloud), and evaluate cloud configuration against best practices. It enables the ability to manage risk throughout multi-cloud infrastructures, provides regulatory compliance reporting, and integrates remediation into the cloud infrastructure lifecycle automation framework.
FortiCWP Videos
Organizations are increasingly deploying a variety of workloads across multiple clouds. In turn, business-critical data and services are increasingly scattered across this distributed infrastructure. Using the shared responsibility model as a guiding principle, enterprises rely on cloud providers to protect the network, storage, and computing layers, while enterprises own the security for everything that is built, deployed, or stored in the public cloud. Due to multi-cloud adoption, most enterprises maintain heterogeneous environments, with tools from each cloud platform differing significantly.
FortiCWP 4.2 Use Case Demos
FortiCWP Product Details
Risk management enables security teams to focus on high priority issues and take quick remediation actions
Data security provides configuration assessments and analyzes documents inside cloud storage repositories
Traffic analysis and investigation ensures visibility into all cloud resources to identify and monitor application traffic
Threat detection and response delivers continuous threat monitoring across the entire security infrastructure
Gain compliance reports for standards such as PCI, HIPPA, SOX, GDPR, ISO 27001, and NIST